What is SSL protocol? Overview of SSL protocol. Learn SSL Architecture Diagram, SSL Record Protocol, 4 phases of SSL protocol etc. SSL: Secure Socket Layer is a handshake protocol that allows servers and clients to exchange different parameters in encrypted ways over a transport network.
1. SSL Protocol Overview
This post about SSL protocol overview, SSL stands for Secure Socket Layer which is a handshake protocol. In SSL handshake protocol, servers and clients exchange different parameters. This protocol performs its various job before application data is transmitted. There are a lot of steps and things run behind this protocol. SSL is a protocol that is used to send encrypted data over the transport network.
For an understanding of SSL (Secure Socket Layer), you should know, why you need SSL and how it helps in security? and what SSL does? You will learn what SSL protocol does but, why you need SSL and how it helps in security challenges, you can find these things in my another post i.e. Web Security threat challenges and solutions and you visit for more knowledge about SSL and security.
If you are curious about, how SSL protocol works then this post is appropriate for your. You can go through step by step and understand SSL (Secure Socket Layer) in details by different visual images or you can say from different perspectives.
2. Key points of SSL protocol
- SSL (Secure Sockets Layer) is a standard security protocol which is used for establishing encrypted links between a web server and a browser in an client server communication, you can say online communication .
- SSL ensures that all data transmitted between the Client and Server (web server and browser) remains encrypted. It works on top of Transport Layer in the network.
- The purpose of SSL is to enhance the capability of TCP with confidentiality, data integrity, server authentication and client authentication features to protect from the security threats.
- It was developed by Dr. Taher ElGamal, present security CTO of salesforce.com during his Netscape tenure during 1995-98.
- SSL is often used to provide security to transactions that take place over HTTP. However, because SSL secures TCP, it can be employed by any application that runs over TCP. Security having application independence is the prime motivation behind SSL.
- SSL provides a simple Application Programmer Interface (API) with sockets, which is similar and analogous to TCP’s API. When an application wants to employ SSL, the application includes SSL classes/libraries.
- Its follow-on standard known as Transport Layer Security (TLS) is defined in IETF RFC-5246
- You required an SSL certificate to create SSL connection. For enabling SSL with HTTP , no changes on Application level. You would need to give all details about the identity of your website and your company as and when you choose to activate SSL on your web server. Two cryptographic keys are created: a Private Key and a Public Key. Objective of private key and public key will be discussed in another post
3. SSL Architecture Diagram
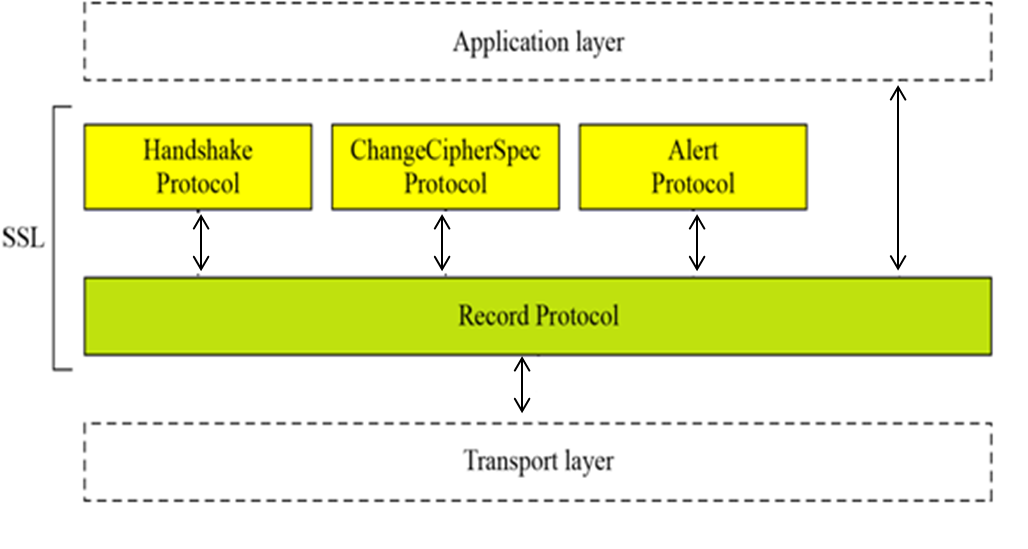
Let us understand the SSL architecture diagram and go through a high level of SSL Architecture, SSL is not a single layer protocol, SSL is two-layered protocols, on the top, there is an application layer and on the bottom, there is a Transport layer. When you review, SSL record protocol, you realized that there are three protocols on top of the SSL record protocol. SSL Record protocol provides services to these three protocols. Application layers interact with record protocol and in turn provide three protocols for different aspects.
- SSL Handshake Protocol allows server and client to exchange different security parameters. This protocol performs its job before application data is transmitted
- SSL Change Cipher Spec Protocol is used to update the cipher suite to be used for the connection.
- SSL Alert Protocol is used to convey SSL related alarms to the peer entities (client and server).
- SSL Record Protocol provides basic security services to the different application layer protocols. e.g. HTTP uses SSL to provide secure Web client/server interactions.
4. SSL Record Protocol
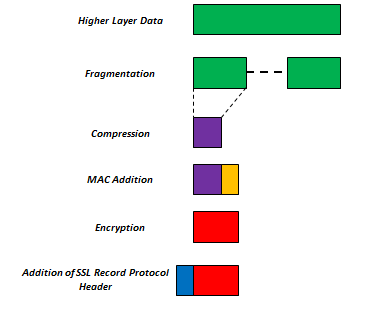
As you know SSL is a record protocol. All security feature applied on data, step by step process as:
- Fragmentation of Data: first of all each application layer data is fragmented into different fragment depending on size of data, let say entire data is fragmented into
2 raise to power 14 bytes - compression: then lossless compression is applied on data this is optional.
- MAC: in this step MAC (message authentication code) is calculated and added with data to maintain message integrity.
- Encryption: in this step resulting packet will be encrypted by using symmetric key encryption with provided parameters.
- Addition of SSL record protocol: in this last step, SSL record protocol header will be added to the packet with data packet.
- And finally, packet is sent to the below Transport Layer.
5. Overview of Four Phases of SSL Handshake
- Phase-1: Establishing Securing Capabilities
- Phase-2: Server Authentication and Key Exchange
- Phase-3: Client Authentication and Key Exchange
- Phase-4: Finalizing Handshake Protocol
For more details visit 4 phases of SSL Protocol.
Your comments are welcome to improve this post. Happy Learning 🙂
good explanation in this post